OpenSea listing exploit
OpenSea, the popular NFT marketplace, was struck by a devastating loophole earlier this week. This was a listing exploit that has allowed opportunists to snipe rare NFTs for well below market value, which they then flip for exuberant profits – with one hacker making over $1,000,000 AUD.
Following this significant incident, Elliptic (blockchain security company), Rotem Yakir (DeFi developer), and several other Twitter users have gone to Twitter to discuss the bug.
What’s the impact of the exploit so far?
Elliptic, the blockchain security company, reported that the exploit was used to steal over $1.5 million AUD worth of NFTs. A screenshot posted by the security company revealed one of the culprits: ‘jpegdegenlove’, who purchased multiple NFTs (including Bored Ape Yacht Club, Mutant Ape Yacht Club, Cool Cats and Cyberkongz) for a significantly discounted $187,000 AUD. They then flipped the snatched NFTs for a whopping $1.3 million.
One of the victims was ‘TBALLER.eth’, who on January 24th tweeted that their Bored Ape Yacht Club NFT had sold for 0.77 ETH, despite them not having it listed. Furthermore, the Bored Ape Yacht Club NFT was at the time going for around 86 ETH, which means they lost $300,000 AUD overnight.
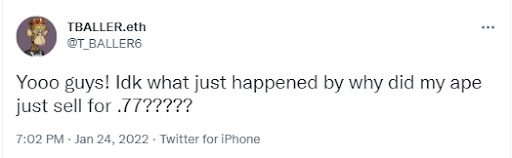
Source: Twitter
Tom Robinson, the co-founder of Elliptic, sums it up succinctly: “It’s a subjective thing whether you consider this to be a loophole or a bug, but the fact is that people are being forced into sales at a price they wouldn’t otherwise have accepted right now,” said Tom Robinson, chief scientist and co-founder of Elliptic.
What exactly is the cause?
Rotem Yakir (DeFi developer) explains what is behind this loophole, citing a mismatch between the information within the NFT smart contracts and the information in OpenSea’s UI.
OpenSea users would commonly transfer their NFT to another wallet, and then back to the original wallet. This was a trick that allowed them to skirt around the expensive ‘gas fees’ required to cancel their first listing – but it wasn’t without its drawbacks. While this technique removed the original listing from the frontend, the original contract would still technically still persist and could be found through the OpenSea API. Specifically, the listing would be listed on Rarible (an NFT platform that aggregates OrderSea listings) at its original price, allowing for opportunists to snipe them at a bargain – as this week has shown.
The kicker on top of all this is that this loophole seems to have been present as early as December 31st – and was even documented on January 12th. The fact that this was then used two weeks later to snipe millions of dollars worth of NFTs from unsuspecting users overnight is, concerning, to say the least.
How is OpenSea proceeding?
Shortly after the loophole was brought to light, OpenSea sent out a tweet announcing the launch of a new listings manager. This new manager should (hopefully) circumvent the listing mismatch issue, and prevent further exploits. On top of this, they have allegedly been reaching out and reimbursing affected users (according to a spokesperson who spoke with ZDNet).
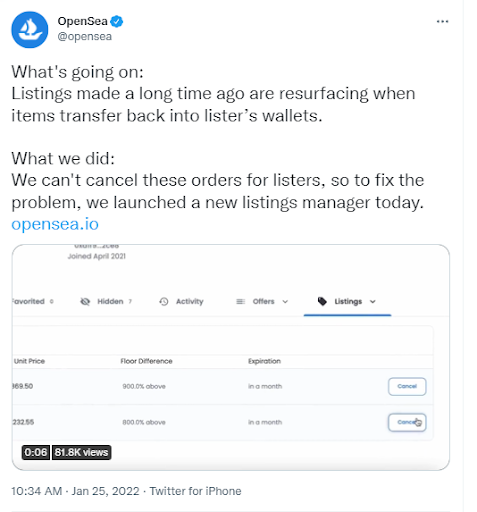
Source: Twitter
Maintaining public goodwill is especially critical now that they’ve recently acquired Dharma (Ethereum wallet project), and given that this isn’t OpenSea’s first security scandal, anything short of thorough reimbursement would be insufficient.














