An analysis conducted by Cisco’s Talos Intelligence has revealed that hackers have been using a Windows tool to deploy cryptocurrency-mining malware since November 2021. The attackers are exploiting Windows Advanced Installer, an application designed to assist developers in packaging other software installers, such as Adobe Illustrator. This exploitation enables them to execute malicious scripts on compromised machines.
According to a blog post dated September 7, the software installers impacted by these attacks are primarily used in 3D modelling and graphic design. Moreover, a noteworthy observation is that most software installers involved in this malware campaign are written in French. This discovery suggests that the victims are likely spread across various business sectors, including architecture, engineering, construction, manufacturing, and entertainment, particularly in French-speaking regions.
The targeted attacks are predominantly concentrated in France and Switzerland, with isolated infections detected in other countries, including the United States, Canada, Algeria, Sweden, Germany, Tunisia, Madagascar, Singapore, and Vietnam. This information is derived from DNS request data sent to the attacker’s command and control host.
Talos Intelligence’s investigation into this illicit crypto-mining campaign has revealed the use of malicious PowerShell and Windows batch scripts to execute commands and establish a backdoor on the victim’s machine. Notably, PowerShell operates in the system’s memory rather than the hard drive, making it challenging to detect such attacks.
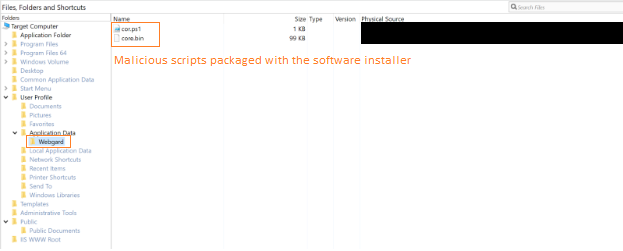
Once the backdoor is established, the attacker executes additional threats, including the Ethereum crypto-mining program PhoenixMiner and lolMiner, a multicoin mining threat. These malicious scripts are executed using Advanced Installer’s Custom Action feature, which allows users to predefine custom installation tasks.
The final payloads, PhoenixMiner and lolMiner, are publicly available miners that leverage the GPU capabilities of computers for cryptocurrency mining.
Cryptocurrency-mining malware is commonly called crypto-jacking, a practice in which cryptocurrency-mining code is surreptitiously installed on a device without the user’s consent or knowledge to illicitly mine cryptocurrencies. Indications of mining malware activity may include device overheating and reduced performance.
Notably, using malware families to compromise devices for cryptocurrency mining or theft is not a novel practice. Recently, BlackBerry, a former smartphone giant, identified malware scripts actively targeting various sectors, including financial services, healthcare, and government.














