Solana memecoins creation tool Pump.fun has claimed that a former employee exploited the platform for nearly $2 million through a “bonding curve” attack.
In a May 16 X post, pump.fun explained that the ex-employee abused their “privileged position” to access a “withdraw authority” and compromise the protocol’s internal systems.
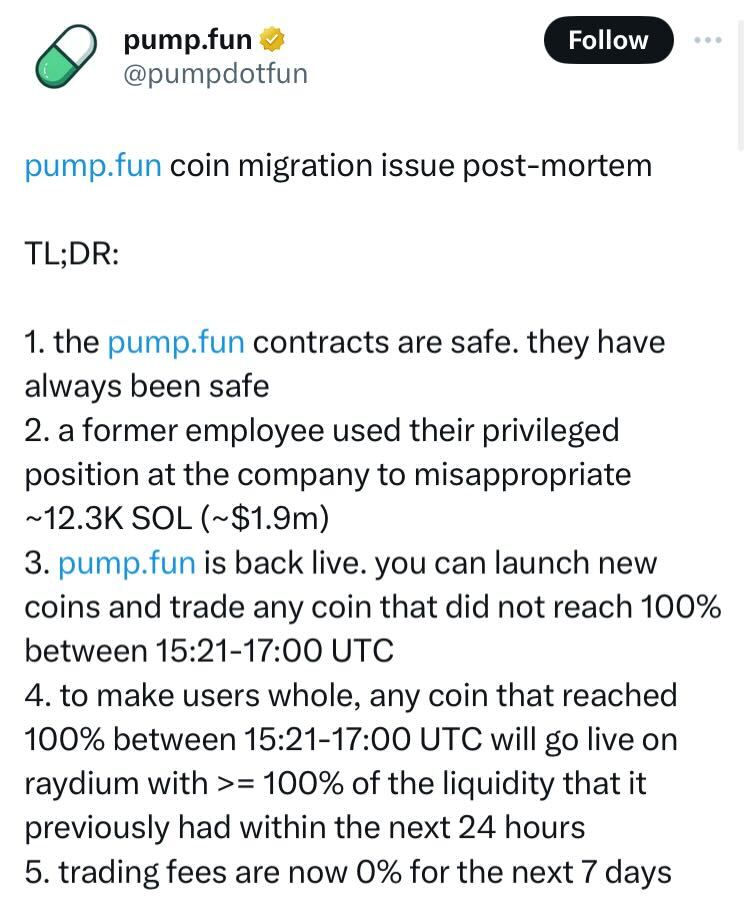
About $1.9 million from the $45 million held in pump.fun’s bonding curve contracts was stolen after the exploit. Trading was temporarily paused following the incident but has since resumed. Pump.fun assured users that its smart contracts remain secure and promised that those affected would receive “100% of the liquidity” they previously held within 24 hours.
Igor Igamberdiev, head of research at cryptocurrency market maker Wintermute, had earlier suggested the hack resulted from an internal private key leak, implicating X user “STACCoverflow.” In a series of cryptic posts, STACCoverflow hinted at their involvement, expressing indifference towards the consequences and stating they were “already fully doxxed.”
Pump.fun has stated that it is cooperating with law enforcement but has not disclosed the name of the former employee involved and did not immediately respond to requests for comment.
Details of the Attack
The alleged exploiter utilised flash loans from the Solana lending protocol Raydium to borrow Solana tokens. These tokens were used to purchase as many coins as possible on pump.fun. When the coins reached 100% on their bonding curves, the exploiter accessed the bonding curve liquidity to repay the flash loans. In total, approximately 12,300 SOL, valued at $1.9 million, was stolen between 3:21 pm and 5:00 pm UTC on May 16.
Pump.fun confirmed that users affected during this period would recover 100% or more of their liquidity held prior to the attack.














