MetaMask vulnerability flagged
2022 has not had a pleasant start regarding security in the crypto space. From the recent Opensea bug with millions worth of NFTs stolen to 3 million emails leaked from CoinMarketCap, to a hacker stealing over 6000 Coinbase accounts.
Today’s security shortcoming hasn’t happened yet – but may still come to pass depending on how MetaMask proceeds. On January 21st, cryptographer and security analyst Alexandru Lupascu flagged a critical vulnerability in MetaMask that gives hackers a way to access users’ IP addresses.
Lupascu, who co-founded the privacy node service OMNIA Protocol, addresses this in his blog post, analysing and showcasing a security loophole that could compromise the privacy and safety of MetaMask’s 21 million users. The cost to pull off this exploit? As low as $50.
How does the loophole work?
According to Lupascu, a malicious party can mint an NFT and then transfer free ownership to an unsuspecting victim with nothing more than their Ethereum address (which is linked to the MetaMask wallet). Usually, there should be nothing wrong with this – however, the problem lies within the data fetching process, in which a user’s IP can be leaked with the proper setup.
The MetaMask mobile app displays NFTs stored in an address using a URL function call to the image data stored on remote servers. Fetching this data (i.e. displaying what NFTs are contained in the Ethereum wallet) is done through a standard HTTP request. All server gateways handling the transmission will also receive the user’s IP information. This is usually a secure process; however, Lupascu demonstrates that hackers can easily exploit it.
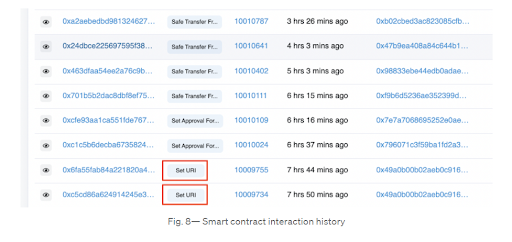
Lupasco begins by minting a new NFT on OpenSea (using the ERC-1155 standard). Then with a smart contract editor (Remix Ethereum IDE in Lupascu’s case), he can alter the original URL linked with the NFT, changing it to connect to a new self-controlled server.
Source: Medium @alxlpsc
With these changes, the IP information of any user that receives this NFT will be made completely visible to Lupascu; all for as low as $50. Hackers can essentially replicate this process and airdrop these NFTs to any MetaMask-connected Ethereum address on a mobile phone, gaining the IP information of any user.
Source: Medium @alxlpsc
However, it’s not limited to cyber attacks either, with Lupascu mentioning that if hackers access more information from the IP address (geolocation, GSM carrier etc.), dangers will extend to physical risks, such as kidnapping.
What is MetaMask doing about this?
The short answer is not much yet. The keyword being yet.
The long answer is that this issue has been widely known for a while now. Lupasco notified the MetaMask team about this vulnerability back in December 14 2021, to which the MetaMask team promised a patch by Q2 2022, which Lupasco found “unacceptable” – which isn’t unwarranted. According to him, an attack utilising this vulnerability would be more devastating than any Distributed Denial of Service (DDoS) attack. It would be a whopping 8X more powerful than 2016’s Mirai DDoS attack that almost took down the entire internet.
However, with Lupascu’s most recent blog post bringing this issue back to the forefront, things are looking brighter. In a recent tweet, Dan Finlay (Founder of MetaMask) declared that they would begin working on finding a solution.
Yeah, I think this issue has been widely known for a long time, so I don’t think a disclosure period applies. Alex is right to call us out for not addressing it sooner. Starting work on it now. Thanks for the kick in the pants, and sorry we needed it. https://t.co/SeKMRKSUGN
— Dan Finlay 🦊💙 (@danfinlay) January 20, 2022